Global Spying Scheme: Hackers Target Sensitive Entities Across 37 Countries
An Asian cyber-espionage group has spent the past year infiltrating computer systems belonging to governments and critical infrastructure organizations across more than 37 countries, according to cybersecurity firm Palo Alto Networks, Inc.
The state-aligned attackers have successfully breached the networks of 70 organizations, which include five national law enforcement and border control agencies. Additionally, they have compromised three ministries of finance, a national parliament, and a senior elected official in another country, as detailed in a recent research report from the firm. Palo Alto Networks, based in Santa Clara, California, has chosen not to disclose the hackers’ country of origin.
This extensive spying operation has allowed the hackers to gather sensitive information, seemingly in alignment with significant geopolitical events such as diplomatic missions, trade negotiations, political unrest, and military actions. The report indicates that the attackers utilized their access to monitor emails, financial transactions, and communications related to military and police operations. They also stole information concerning diplomatic matters, often remaining undetected in some systems for months.
“They employ highly-targeted and tailored phishing emails, along with known unpatched security vulnerabilities, to infiltrate these networks,” stated Pete Renals, director of national security programs at Unit 42, Palo Alto Networks’ threat intelligence division. “Espionage appears to be the primary motivation behind these attacks, as the actors frequently seek access to email communications and other sensitive data.”
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) is aware of this campaign and is collaborating with partners to prevent hackers from exploiting the vulnerabilities identified in the report, according to Nick Andersen, CISA’s executive assistant director for cybersecurity.
Representatives from the FBI and CIA have declined to comment, while the NSA did not respond to a request for comment.
Palo Alto Networks researchers confirmed that the group successfully accessed and exfiltrated sensitive data from some victims’ email servers. The firm has notified the affected organizations and offered assistance, a rare move for a cybersecurity company. Some of the victims were identified in the report, which is unusual in the industry.
Notably, some of the hackers’ activities coincided with events of particular significance to the Chinese government. For instance, one suspected breach occurred the day after U.S. military and law enforcement captured Venezuelan leader Nicolas Maduro. As early as January 4, the hackers “likely compromised” a device linked to a facility operated by Venezolana de Industria Tecnológica, a joint venture between Venezuela’s government and an Asian tech firm. The organization did not respond to an email seeking comment.
Another hacking campaign targeted government entities in the Czech Republic. In July 2025, Czech President Petr Pavel met with the Dalai Lama, and shortly thereafter, the hackers conducted reconnaissance on Czech government targets, including the Army, police, Parliament, and the Ministry of Foreign Affairs. The Czech cybersecurity agency, the National Cyber and Information Security Authority, did not respond to a request for comment on the report. The Chinese Embassy in Prague has previously dismissed allegations of attacks against the Czech Republic as “unsubstantiated.”
The hacking group also compromised Brazil’s Ministry of Mines and Energy, a significant source of rare earth mineral reserves. This breach coincided with U.S. diplomats meeting with mining executives in the country. An official at the ministry stated that they had not identified any attack.
According to the report, the hackers are also suspected of operating in Germany, Poland, Greece, Italy, Cyprus, Indonesia, Malaysia, Mongolia, Panama, and other countries.
Recently, the Chinese government prohibited companies in the country from using products from Palo Alto Networks, along with security technologies from over a dozen other U.S. and Israeli vendors, as per a government directive seen by Bloomberg News.
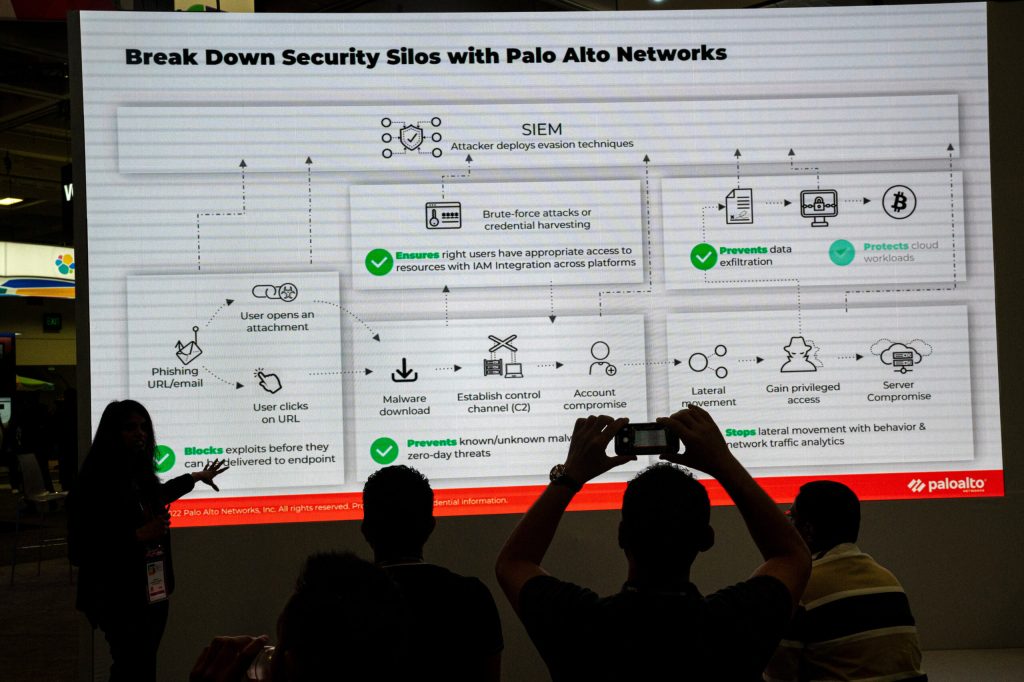
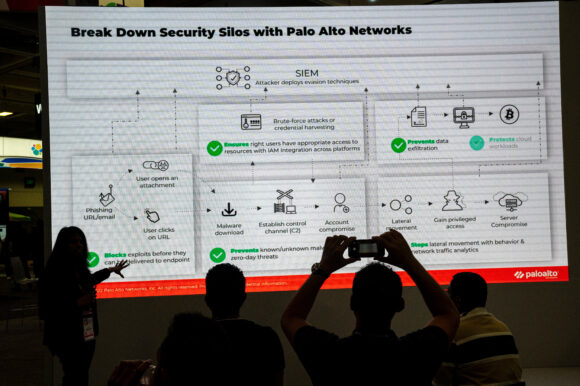
Photograph: Attendees watch a presentation at the Palo Alto Networks booth during the RSA Conference in San Francisco, California, on Wednesday, April 26, 2023. Photo credit: David Paul Morris/Bloomberg
Copyright 2026 Bloomberg.
Topics
Cyber
Interested in Cyber?
Get automatic alerts for this topic.
An Asian cyber-espionage group has spent the past year infiltrating computer systems belonging to governments and critical infrastructure organizations across more than 37 countries, according to cybersecurity firm Palo Alto Networks, Inc.
The state-aligned attackers have successfully breached the networks of 70 organizations, which include five national law enforcement and border control agencies. Additionally, they have compromised three ministries of finance, a national parliament, and a senior elected official in another country, as detailed in a recent research report from the firm. Palo Alto Networks, based in Santa Clara, California, has chosen not to disclose the hackers’ country of origin.
This extensive spying operation has allowed the hackers to gather sensitive information, seemingly in alignment with significant geopolitical events such as diplomatic missions, trade negotiations, political unrest, and military actions. The report indicates that the attackers utilized their access to monitor emails, financial transactions, and communications related to military and police operations. They also stole information concerning diplomatic matters, often remaining undetected in some systems for months.
“They employ highly-targeted and tailored phishing emails, along with known unpatched security vulnerabilities, to infiltrate these networks,” stated Pete Renals, director of national security programs at Unit 42, Palo Alto Networks’ threat intelligence division. “Espionage appears to be the primary motivation behind these attacks, as the actors frequently seek access to email communications and other sensitive data.”
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) is aware of this campaign and is collaborating with partners to prevent hackers from exploiting the vulnerabilities identified in the report, according to Nick Andersen, CISA’s executive assistant director for cybersecurity.
Representatives from the FBI and CIA have declined to comment, while the NSA did not respond to a request for comment.
Palo Alto Networks researchers confirmed that the group successfully accessed and exfiltrated sensitive data from some victims’ email servers. The firm has notified the affected organizations and offered assistance, a rare move for a cybersecurity company. Some of the victims were identified in the report, which is unusual in the industry.
Notably, some of the hackers’ activities coincided with events of particular significance to the Chinese government. For instance, one suspected breach occurred the day after U.S. military and law enforcement captured Venezuelan leader Nicolas Maduro. As early as January 4, the hackers “likely compromised” a device linked to a facility operated by Venezolana de Industria Tecnológica, a joint venture between Venezuela’s government and an Asian tech firm. The organization did not respond to an email seeking comment.
Another hacking campaign targeted government entities in the Czech Republic. In July 2025, Czech President Petr Pavel met with the Dalai Lama, and shortly thereafter, the hackers conducted reconnaissance on Czech government targets, including the Army, police, Parliament, and the Ministry of Foreign Affairs. The Czech cybersecurity agency, the National Cyber and Information Security Authority, did not respond to a request for comment on the report. The Chinese Embassy in Prague has previously dismissed allegations of attacks against the Czech Republic as “unsubstantiated.”
The hacking group also compromised Brazil’s Ministry of Mines and Energy, a significant source of rare earth mineral reserves. This breach coincided with U.S. diplomats meeting with mining executives in the country. An official at the ministry stated that they had not identified any attack.
According to the report, the hackers are also suspected of operating in Germany, Poland, Greece, Italy, Cyprus, Indonesia, Malaysia, Mongolia, Panama, and other countries.
Recently, the Chinese government prohibited companies in the country from using products from Palo Alto Networks, along with security technologies from over a dozen other U.S. and Israeli vendors, as per a government directive seen by Bloomberg News.
Photograph: Attendees watch a presentation at the Palo Alto Networks booth during the RSA Conference in San Francisco, California, on Wednesday, April 26, 2023. Photo credit: David Paul Morris/Bloomberg
Copyright 2026 Bloomberg.
Topics
Cyber
Interested in Cyber?
Get automatic alerts for this topic.




